Strategic Data Governance and Risk Management in Enterprise Architecture
Discover how the synergy between proactive data governance and defensive risk management forms the bedrock of modern business resilience and architectural excellence.

Every byte of data an organization generates is a double-edged sword: it is either the strategic fuel powering the next great innovation or a dormant liability capable of disrupting an entire operation. In an era where a single security lapse or compliance failure can dismantle decades of corporate reputation, the synergy between data governance and risk management has evolved from a back-office necessity into the bedrock of business resilience. This intersection is not merely a bureaucratic hurdle, but a sophisticated architectural discipline essential for sustainable growth in an increasingly intelligent world.
Is Data Governance the Same as Data Risk Management?
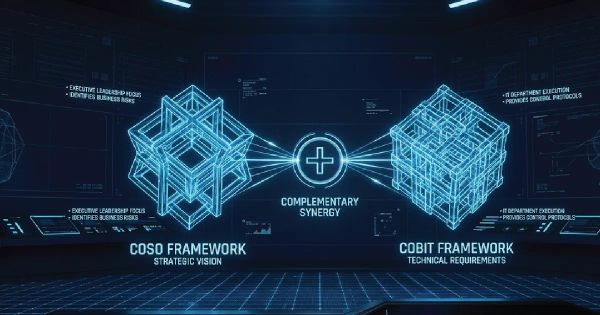
A common point of confusion in executive suites is the distinction between governance and risk management. While they are inextricably linked, they represent different sides of the same coin.
Data Governance is the proactive exercise of authority and control over the management of data assets. It defines the "who, what, and how" of data—establishing policies for quality, availability, and usability. It is essentially the proactive framework that ensures data serves the business's strategic objectives.
Conversely, Data Risk Management is the defensive posture an organization adopts to identify, assess, and mitigate threats associated with that data. This includes everything from cybersecurity breaches to regulatory non-compliance and ethical lapses in AI model training.
| Feature | Data Governance (Proactive) | Data Risk Management (Defensive) |
|---|---|---|
| Primary Goal | Optimization & Value Creation | Protection & Loss Prevention |
| Core Activities | Policy setting, quality, stewardship | Threat assessment, mitigation, recovery |
| Focus | How we should use data | What could go wrong with data |
| Ownership | Business Owners & Stewards | CISO & Security Teams |
The synergy between these two disciplines is where true value lies. Without a Governance strategy, risk management is a series of reactive fire-drills. Without risk management, governance is a toothless set of guidelines. A mature data governance and risk management strategy ensures that every byte of data is accounted for, secured, and utilized within a clear ethical and legal framework.
Why Should Enterprise Architecture Prioritize Governance-Led Risk Mitigation?
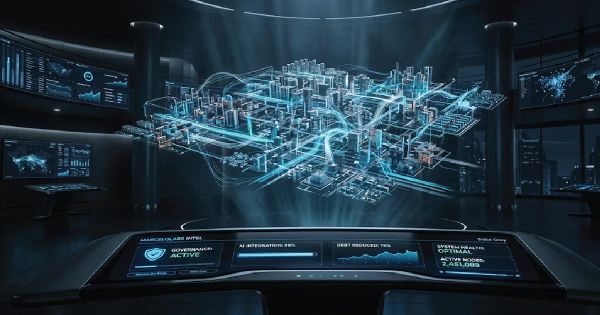
Modern Architecture is no longer just about connecting systems; it is about orchestrating the flow of trust. When we integrate governance directly into the architectural blueprint, we move toward "Compliance by Design."
From a technical perspective, this involves the implementation of robust metadata management and automated data lineage. By understanding the provenance of data—where it originated, how it was transformed, and where it resides—architects can pinpoint vulnerabilities before they are exploited. According to the Data Management Association (DAMA), organizations that fail to integrate these two disciplines face significantly higher costs in data recovery and regulatory fines.

Integrating data governance and risk management at the architectural level allows for:
- Immutable Data Lineage: Ensuring that every transformation is logged and auditable using tools like OpenLineage.
- Granular Access Control: Moving beyond simple passwords to Attribute-Based Access Control (ABAC), a standard recommended by NIST.
- Schema Evolution Management: Preventing "data swamps" through strict version control of data structures.
How Can Organizations Quantify Data Risks Within a Governance Framework?
One of the greatest challenges in Operations is quantifying the "invisible" risk. To manage risk effectively, it must be measurable. A consultative approach to risk assessment involves categorizing data into tiers based on sensitivity (e.g., Public, Internal, Confidential, Restricted).
To calculate these scores, we look at:
- Probability Assessment: What is the likelihood of a data breach or a quality failure? This is often calculated through historical analysis and threat modeling.
- Impact Analysis: If a specific dataset were compromised, what would be the financial, reputational, and legal cost?
- Governance Maturity Scoring: Does the organization have active Data Stewards? Are data quality metrics reviewed monthly?
By assigning a "Risk Score" to every major data domain, leadership can prioritize investments in Security and reengineering efforts where they are most needed.
The Role of Reengineering in Eliminating Legacy Governance Gaps
Many organizations struggle because their governance policies are 21st-century, but their infrastructure is stuck in the late 90s. Reengineering is often the only path forward.

Legacy systems often lack the hooks for modern API-based governance tools. In these cases, we recommend a "Strangler Fig" pattern—gradually wrapping legacy data stores in modern governance layers. This allows for real-time monitoring and policy enforcement without needing to rip and replace mission-critical systems overnight. This technical transition is vital for maintaining high standards during periods of high-growth or digital transformation.
Navigating the Compliance Labyrinth: GDPR, CCPA, and Beyond
In a globalized economy, risk management is synonymous with regulatory agility. Whether it is the stringent requirements of the EU GDPR or the evolving landscape of the California Consumer Privacy Act (CCPA), data governance provides the evidence required for compliance.
Technical controls such as Encryption at Rest and in Transit, Data Masking, and Tokenization are the tactical tools used to enforce governance policies. However, the strategy must also account for "The Right to be Forgotten" and data portability. A robust governance engine automates these requests, turning a potential legal nightmare into a standard operational procedure.
Emerging Trends: AI, DataOps, and the Future of Risk
As we look toward the future, the integration of Artificial Intelligence into data governance and risk management is inevitable. AI can scan petabytes of data to find anomalous patterns that suggest a slow-leak breach or data degradation.
Furthermore, the rise of DataOps—the fusion of data engineering with DevOps principles—is automating the governance lifecycle. We advocate for "Data Governance as Code." By defining governance policies in version-controlled repositories (similar to Terraform for Infrastructure), they can be tested and deployed just like software, ensuring that security and risk management are "shifted left" in the development cycle.
Conclusion: Building the Fortress of the Future
Mastering data governance and risk management is not a destination; it is a continuous state of operational excellence. It requires a holistic view that spans across your organization’s architecture, security protocols, and operational workflows.
By treating data as a high-stakes asset that requires both a proactive steering committee and a rigorous defensive shield, you position your enterprise not just to survive in the digital age, but to lead it.