How to Choose a SOC 2 Auditor: A Strategic Guide for the CISO
Your SOC 2 report is only as strong as the reputation of the firm that signs it. This strategic guide helps CISOs evaluate auditors based on technical alignment, industry expertise, and enterprise value.

In the modern SaaS economy, trust is the ultimate currency. As organizations move more data to the cloud, a SOC 2 report has evolved from a "nice-to-have" badge into a critical sales enablement tool and a prerequisite for enterprise contracts. However, the value of your SOC 2 attestation is only as strong as the reputation of the firm that signs it.
For security leaders, determining how to choose a soc 2 auditor for ciso success involves more than just a price comparison; it is a strategic decision that impacts your security posture, your timeline to market, and your brand’s credibility. This guide provides a sophisticated framework for selecting a partner that aligns with your technical environment and business objectives.
What is the role of a SOC 2 auditor in the compliance process?
Before diving into selection criteria, it is essential to define what a SOC 2 auditor actually does. Unlike a simple security scan, a SOC 2 examination is an attestation performed by a licensed CPA (Certified Public Accountant) firm.
The auditor’s primary responsibility is to provide an independent opinion on whether your organization’s controls are designed effectively (Type I) and operating consistently over time (Type II) based on the AICPA Trust Services Criteria (TSC). They act as a neutral third party that validates your claims to your customers, ensuring that your descriptions of your systems are accurate and your security practices are rigorous.

Why is selecting the right CPA firm critical for your organization?
Not all SOC 2 reports carry the same weight in an enterprise procurement office. A report issued by a firm with deep technical expertise and a strong peer-review record provides high assurance to your stakeholders. When researching how to choose a soc 2 auditor, a CISO must recognize that choosing a "check-the-box" partner can lead to several risks:
- Audit Fatigue: An auditor who doesn't understand your tech stack will request irrelevant evidence, wasting hundreds of hours of your engineering team’s time.
- Reputational Risk: Sophisticated buyers often scrutinize the auditing firm. If the firm is known for low-quality, automated "commodity" audits, your SOC 2 may be met with skepticism.
- Scope Creep: An inexperienced auditor may struggle to define the "system boundary," leading to an unnecessarily complex audit that covers systems irrelevant to your service commitments.

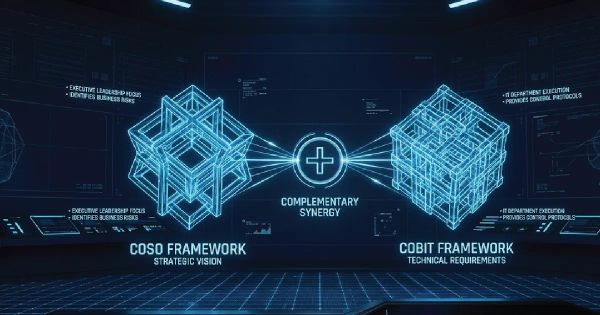
To ensure your compliance journey supports your broader risk management strategy, you should view SOC 2 as part of a larger ecosystem. For a deeper dive into how different standards interact, see our common security framework guide.
How to choose a SOC 2 auditor for CISO requirements and tech stacks?
One of the most frequent complaints from CISOs is that their auditors "don't speak cloud." When evaluating how to choose a soc 2 auditor for ciso leadership, technical alignment is paramount.
If your organization is cloud-native, utilizing microservices, serverless architecture, and automated CI/CD pipelines, you cannot rely on an auditor who primarily works with legacy on-premise infrastructure. You need a firm that understands:
- Infrastructure as Code (IaC): Can they audit Terraform or CloudFormation scripts?
- Ephemeral Environments: Do they understand how controls apply to containers and Kubernetes?
- Automated Evidence Collection: Are they comfortable using GRC (Governance, Risk, and Compliance) platforms to pull data via API, or are they still asking for manual screenshots?
What are the key criteria for evaluating potential SOC 2 audit firms?
To move beyond a superficial evaluation, use the following five pillars to vet your prospective partners.
1. Peer Review and AICPA Affiliation
A SOC 2 report must be signed by a licensed CPA firm. However, you should go a step further and ask for their latest Peer Review Report. The AICPA requires CPA firms to undergo a peer review every three years to ensure their auditing practices meet the highest standards. A firm that is "pass with deficiencies" or has no record of a recent review should be a major red flag for any security executive.
2. Industry-Specific Experience
Security requirements for a Fintech company differ vastly from those of a Healthcare SaaS or an AI-driven data processor. When considering how to choose a soc 2 auditor, ask potential partners:
- "How many SOC 2 audits have you completed for companies with a similar headcount and data volume in our specific niche?"
- "Can you provide redacted sample reports for a similar organization?"
3. The "Partner-to-Staff" Ratio
Many large firms will use a "bait and switch" tactic: a highly experienced partner sells you the engagement, but the actual fieldwork is performed by junior associates who are learning on your time. Inquire about the specific team that will be handling your audit. A firm where a partner or senior manager is deeply involved in the day-to-day evidence review will provide a much smoother, more insightful experience for your team.
4. Methodology and Communication Style
A SOC 2 audit is a collaborative effort. Understanding how to choose a soc 2 auditor for ciso workflows involves vetting their specific methodology:
- Readiness Assessment: Do they offer a gap analysis before the official "period of reliance" begins?
- Remediation Guidance: While auditors cannot design your controls (to maintain independence), a high-quality firm will provide clear feedback on why a control failed.
- Communication Cadence: Will there be weekly status meetings, or do they disappear for weeks?
5. Blended Audit Capabilities
If you anticipate needing HIPAA, ISO 27001, or HITRUST in the near future, choosing a firm that can perform "blended" or "integrated" audits is a significant efficiency gain. Testing a control once for multiple frameworks can reduce your team’s workload by up to 40%.
Should you choose a Big Four firm or a boutique SOC 2 auditor?
This is a common dilemma for security leaders. The decision often depends on your target market and budget.
- Big Four (Deloitte, PwC, EY, KPMG): These firms carry immense brand recognition. If you are selling to Global Fortune 50 banks, they may occasionally prefer a Big Four report. However, these audits come with premium pricing and often less personalized attention for mid-market companies.
- Boutique/Specialized Firms: These firms often specialize exclusively in IT attestation. They are usually more agile, more tech-savvy, and offer better "value for money." Because their reputation depends entirely on their security expertise, their reports are often more thorough and technically accurate.

What red flags should you watch for when interviewing auditors?
When researching how to choose a soc 2 auditor, you will encounter many "compliance factories" that promise the world. Be wary of the following:
- Fixed Low-Cost Quotes: If a firm offers a price that seems too good to be true, they are likely cutting corners. They may spend very little time actually testing your controls, which results in a weak report.
- "We provide the controls for you": This is a conflict of interest. An auditor cannot audit their own work. If they promise to write your policies and then audit them, the integrity of the SOC 2 is compromised.
- Lack of a US Presence: For SOC 2, having an auditor with no US-based licensed CPAs can lead to significant delays and potential invalidation of the report.
How much does a SOC 2 audit cost and what influences the price?
While pricing varies, a standard SOC 2 Type II audit typically ranges from $20,000 to $60,000+ for the audit fee alone. When a ciso evaluates how to choose a soc 2 auditor, they must account for:
- The Number of Trust Service Criteria: Security is mandatory, but adding Availability, Confidentiality, Processing Integrity, or Privacy adds complexity.
- Number of Applications/Locations: Auditing a single SaaS product is cheaper than auditing a suite of different platforms.
- Type I vs. Type II: A Type I (point-in-time) is significantly cheaper than a Type II (period-of-time).

Final Thoughts: The Audit is a Partnership
Choosing the right auditor is the difference between a painful, distracting hurdle and a streamlined process that actually improves your organization's security posture. By focusing on technical competency, industry reputation, and clear communication, you ensure that your SOC 2 report becomes a powerful asset for your sales team.
As you prepare for your audit, remember that SOC 2 is just one piece of the puzzle. Understanding the broader landscape of security frameworks is essential for any CISO or executive aiming for long-term resilience and market trust.