
Reengineering
Decoding Composable Commerce: The Definitive Guide for Modern Retail
Discover how composable commerce works, its key benefits, and why enterprise retailers are moving to modular, API-driven architectures.
Managing the coexistence of old and new platforms is a matter of strategic defense. Explore high-level protocols, security audits, and risk management strategies to protect data integrity during complex migrations.

Reengineering
Discover how composable commerce works, its key benefits, and why enterprise retailers are moving to modular, API-driven architectures.

Security
Discover who actually needs ISO 27001 certification in today's zero-trust market, and learn how it accelerates enterprise sales and procurement.

Security
Discover the essential ISO 27001 procedures needed to align security with business objectives, manage risk, and achieve verifiable global compliance.
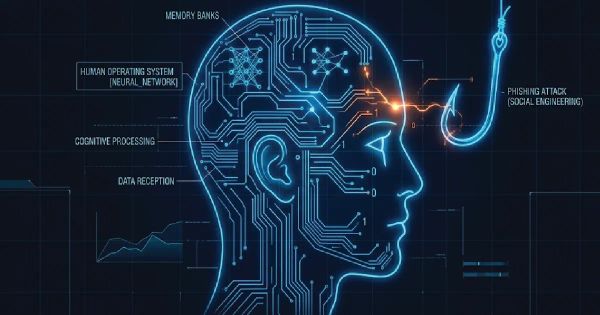
Security
This strategic guide explores the critical difference between phishing and social engineering in 2026, offering C-Suite protocols for Human Risk Management and organizational resilience.

Governance
Explore the core pillars of accountability, data stewardship, and standardization to transform your digital presence into a competitive

Reengineering
Discover how the synergy between proactive data governance and defensive risk management forms the bedrock of modern business resilience and architectural excellence.
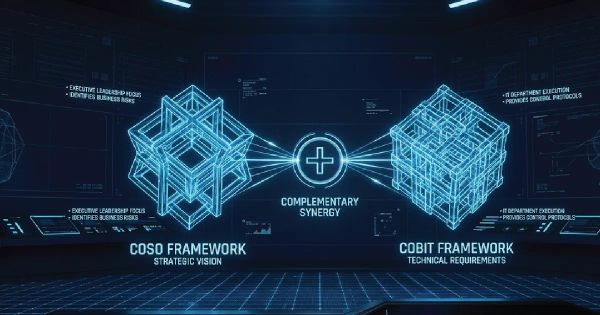
Governance
Explore the essential differences, similarities, and integration of the COSO and COBIT frameworks for modern risk management.

Security
Your SOC 2 report is only as strong as the reputation of the firm that signs it. This strategic guide helps CISOs evaluate auditors based on technical alignment, industry expertise, and enterprise value.

Security
Stop losing control of your data in the cloud. Discover how Enterprise Key Management (EKM) acts as the cryptographic nervous system for modern security architecture and governance.
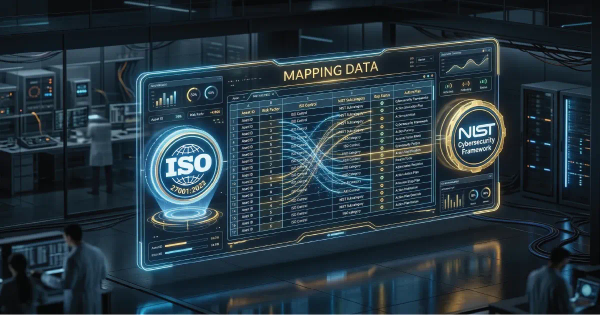
Security
Stop wasting hours on manual cross-referencing. Access the professional ISO 27001:2022 to NIST CSF 2.0 mapping tool designed for elite security architects.

Security
Cybersecurity is no longer just an IT problem—it’s a board-level liability. Learn why a common security framework is your ultimate strategic defense.