Phishing vs Social Engineering: A Strategic Executive Guide to Human Risk
This strategic guide explores the critical difference between phishing and social engineering in 2026, offering C-Suite protocols for Human Risk Management and organizational resilience.
Most sophisticated firewall in the world cannot protect an organization if its employees are manipulated into opening the gate. As we navigate 2026, the convergence of artificial intelligence and psychological manipulation has elevated the conversation around phishing vs social engineering from a technical IT concern to a primary boardroom imperative.
For the C-Suite, understanding the nuance between these two concepts is not just about vocabulary; it is about resource allocation and risk mitigation. While the terms are often used interchangeably in casual conversation, they represent different scales of threat and require distinct defensive strategies.
What is Phishing?
At its core, phishing is a digital method of delivering a fraudulent message to a victim. It is a technical implementation of a lure, designed to appear as if it comes from a trusted source.
While historical phishing relied on "spray and pray" tactics—sending millions of generic emails with poor grammar—modern phishing has undergone a paradigm shift. Today, attackers leverage LLMs (Large Language Models) to craft perfect, context-aware communications that bypass traditional email filters.
For an enterprise, phishing usually manifests as:
- Credential Harvesting: Deceptive login pages designed to steal "single sign-on" (SSO) credentials.
- Malware Delivery: Attachments or links that execute ransomware or spyware within the corporate network.
- Business Email Compromise (BEC): Spoofed executive identities used to authorize fraudulent wire transfers.
In the context of cybersecurity, phishing is the medium, but it is powered by the psychological principles of social engineering.
What is Social Engineering?
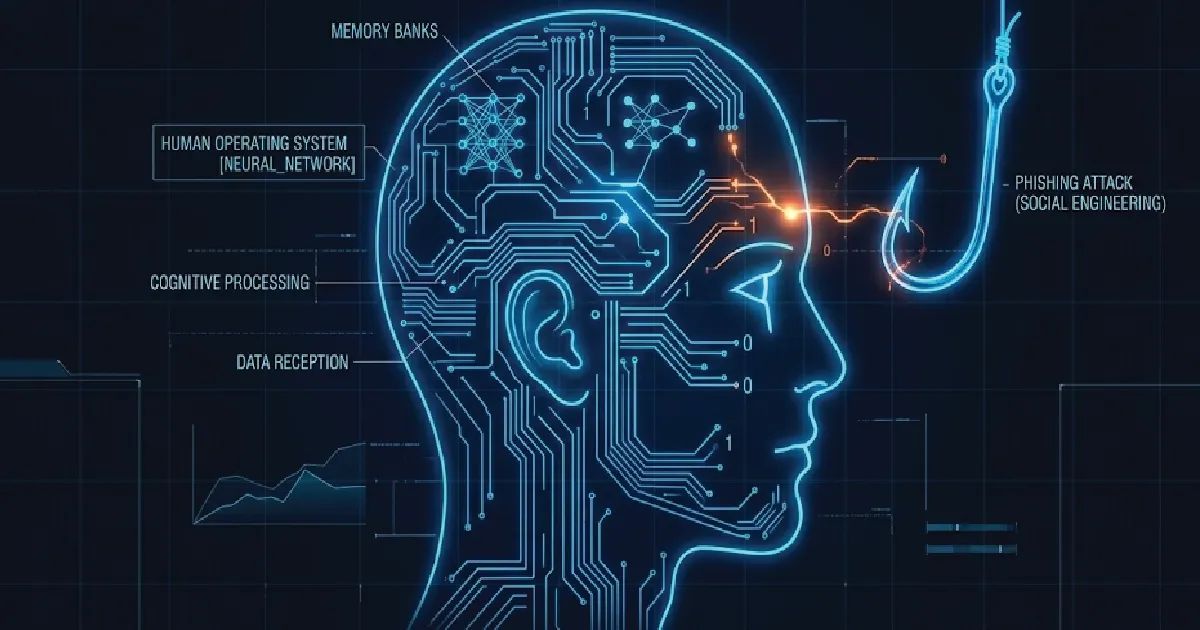
Social Engineering is the broader umbrella of human hacking. It is the art of manipulating people into performing actions or divulsing confidential information. Unlike a technical exploit that targets a software vulnerability, social engineering targets the "Human Operating System."
Social engineers exploit deep-seated human traits: trust, authority, urgency, and fear. It is a psychological game where the attacker researches the target's organizational structure, social media presence, and professional relationships to build a credible narrative.
In a corporate environment, social engineering is not limited to the digital realm. It can occur via a phone call (Vishing), a text message (Smishing), or even an in-person interaction at a secure facility. If cybersecurity is the shield, social engineering is the attempt to convince the person holding the shield to put it down.
Phishing vs Social Engineering: What is the Difference?
Understanding the relationship between phishing vs social engineering is best visualized as a hierarchy.
All phishing is social engineering, but not all social engineering is phishing.
Feature |
Phishing |
Social Engineering (Broad) |
|---|---|---|
Medium |
Primarily Email, SMS, or Web. |
Phone, In-person, Digital, or Physical. |
Complexity |
Often automated and scalable. |
Can be highly manual and deeply researched. |
Objective |
Immediate data theft or malware. |
Long-term access, espionage, or subversion. |
Technicality |
Relies on spoofing and malicious code. |
Relies on psychology and relationship building. |
Cost to Attacker |
Very low (Pennies per 1k emails). |
Medium to High (Requires time and research). |
The fundamental phishing vs social engineering difference lies in the delivery. Phishing is a specific tool, whereas social engineering is the strategy that makes that tool effective. If an attacker calls your CFO pretending to be a bank auditor, that is social engineering. If they send that same CFO an email with a "suspicious activity" link, it is phishing.
Phishing and Other Social Engineering Types of Attacks
To protect an enterprise, leaders must recognize that attackers often use a multi-channel approach. Rarely is a major breach the result of a single isolated email.
- Spear Phishing: A highly targeted version of phishing aimed at specific individuals, often C-suite executives or finance managers. It uses personal details to increase credibility.
- Whaling: A subset of spear phishing that exclusively targets the "Big Fish"—CEOs, CFOs, and Board Members.
- Vishing (Voice Phishing): Using AI-generated voice cloning to impersonate a known colleague or superior over the phone.
- Baiting: Leaving a "free" or labeled physical device (like a USB drive) in a common area, hoping an employee's curiosity will lead them to plug it into the network.
- Quid Pro Quo: An attacker calls an employee pretending to be technical support, offering a "fix" in exchange for login credentials.
- Pretexting: Creating a complex fabricated scenario (the "pretext") to steal data, such as a fake HR audit requiring personal payroll information.

How to Protect Your Enterprise from Phishing and Social Engineering Attacks
A robust cybersecurity posture requires moving beyond simple "compliance training." Enterprises must transition to a Human Risk Management (HRM) framework.
1. Implement Adaptive Authentication
Relying on passwords is no longer viable. Multi-factor authentication (MFA) is the baseline, but "Phishing-Resistant MFA" (using hardware keys like Yubikeys) is the gold standard for high-value targets.
2. Risk-Based Scoring and Monitoring
Modern platforms now allow organizations to assign a "Risk Score" to individual employees based on their behavior—such as their interaction with simulated phishing or their access patterns to sensitive data. This allows for targeted, rather than generic, intervention.
3. AI-Powered Defensive Layers
Since attackers are using AI to craft lures, enterprises must use AI to detect them. Natural Language Processing (NLP) tools can analyze the sentiment and metadata of incoming emails to flag "unusual tone" or "suspicious urgency" that human eyes might miss.
4. Create a "Reporting Culture"
The goal is to move from a culture of fear to a culture of transparency. Employees should feel empowered to report a suspicious interaction immediately without fear of reprimand. Rapid reporting is the difference between a minor incident and a total system breach.
Importance of Preventing These Attacks in an Organization
The cost of ignoring phishing and social engineering threats goes far beyond a temporary IT outage.
- Financial Impact: According to recent industry reports, the average cost of a data breach exceeds $4.5 million, with social engineering-based breaches being among the most expensive due to their depth.
- Brand Equity: Trust is the hardest asset to build and the easiest to lose. A breach resulting from human manipulation suggests a lack of internal controls to partners and clients.
- Regulatory Compliance: With the tightening of GDPR, CCPA, and industry-specific regulations, a failure to demonstrate "reasonable security measures" against social engineering can result in massive legal penalties.
- Operational Continuity: Ransomware delivered via phishing can paralyze a global supply chain in minutes, as seen in numerous high-profile infrastructure attacks.

Conclusion: The Strategic Imperative
In the debate of phishing vs social engineering, the winner is always the attacker if the organization treats these as mere "IT problems."
As a leader, your role is to architect a resilient culture that understands that human psychology is the new perimeter. By investing in Human Risk Management and fostering a sophisticated understanding of these threats at every level of the organization, you transform your greatest vulnerability into your strongest line of defense.
For more insights on architecting secure enterprise migrations and managing technical risk, explore our deep dives at MarceloLabs.